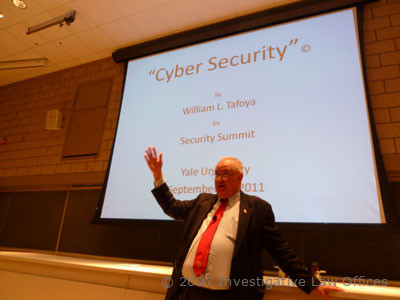
In 2011 the Security Labs team, including Marc Tobias, Tobias Bluzmanis, Matt Fiddler, Tommie Blackwell, Kevin Manson, and Todd Hillis held a two-day physical and cyber-security summit on the campus of Yale University. Students from Yale, MIT, and other schools attended and learned the basics of lock design and bypass. They worked different problems involving security vulnerabilities. William Tafoya, retired Senior FBI official, lectured on Cyber-Security issues.
Lectures and Public Presentations
Waterloo University Quantum Computing Lecture by Marc Tobias
Marc Weber Tobias as Keynote Speaker at the Quantum Computing Conference at Waterloo University, Canada, gave a presentation on physical security.
Cyber-Security And Def Con Presentations
Def Con and Cyber-Security Presentations
Marc Tobias and Tobias Bluzmanis presented for nine years at Def Con on aspects of Physical Security, from 2005-2013. They also presented at Hackers On Planet Earth (HOPE) in New York at several conferences, as well as at Hack In The Box (HITB) in Dubai, UAE and Kuala Lumpur, Malaysia. Below is a partial list of events.
- 2013-08-03 10:00 – DEF CON 21 (2013) – Insecurity – A Failure of Imagination
- 2012-07-27 17:00 – DEF CON 20 (2012) – Safes and Containers: Insecurity Design Excellence
- DEF CON 19 (2011) – Insecurity: An Analysis Of Current Commercial And Government Security Lock Designs
- 2012-07-13 13:00 – HOPE Number Nine (2012) – Using a Space Camp Model for Next Generation Security Training
- 2010-07-31 12:00 – DEF CON 18 (2010) – Insecurity Engineering of Physical Security Systems: Locks, Lies, and Videotape
- 2009-08-02 11:00 – DEF CON 17 (2009) – Invisible Access: Electronic Access Control, Audit Trails and “High Security”
- 2008-08-08 13:00 – DEF CON 16 (2008) – Open in 30 Seconds: Cracking One of the Most Secure Locks in America
- 2008-07-18 18:00 – The Last HOPE (2008) – Undoing Complexity – From Paper Clips to Ball Point Pens
- 2007-08-05 14:00 – DEF CON 15 (2007) – High Insecurity: Locks, Lies, and Liability
- 2006-08-05 17:00 – DEF CON 14 (2006) – Things That Go “Bump” in the night: An Analysis of Current and Emerging Threats to Physical Security
- 2006-07-21 14:00 – HOPE Number Six (2006) – Lockpicking: Exploits for Mechanical Locks
- 2005-07-30 10:00 – DEF CON 13 (2005) – Physical Security Bypass Techniques: Exploring the Ethics of Full Disclosure
- 2004-07-10 21:00 – The Fifth HOPE (2004) – Homeland Security And You: Harry Potter Meets Reality
- 2004-07-10 11:00 – The Fifth HOPE (2004) – Lockpicking
Def Con Lectures 2005-2013 On Security By Marc Weber Tobias And Tobias Bluzmanis
Def Con is the largest cyber-security conference in the world, held in Las Vegas every August. Marc Tobias ans Tobias Bluzmanis lectured on physical security every year from 2005-2013. The media links provide information as to the specific presentation. See the “In the Media” section for related stories in Wired and other publications that covered Def Con.
Read Def Con Chronicles: Gadgets, tech and links by Alex Moskalyuk
__ DefCon @ Gadgets, tech and links
DEF CON 13 2005-
Physical Security Bypass Techniques: Exploring the Ethics of Full Disclosure
Def Con 13 Speakers Information
No video available, only audio link
DEF CON 14 2006 DEF CON 14 (2006) – Things That Go “Bump” in the night: An Analysis of Current and Emerging Threats to Physical Security
DEF CON 14 Speakers Information
Lock picking child’s play at major US computer hackers conference
DEF CON 15 2017 High Insecurity: Locks, Lies, and Liability
DEF CON 16, 2008 OPEN IN THIRTY SECONDS: CRACKING ONE OF THE MOST SECURE LOCKS IN AMERICA
DEF CON 17 2009 “INVISIBLE ACCESS” OPENING NEW DOORS TO INSECURITY
DEF CON 17 Speaker Information
Hacking the Assa Solo Lock – Schneier on Security
DEF CON 18 2010 LOCKS, LIES, AND VIDEOTAPE: Iloq Insecurity
DEF CON 19 LOCK DESIGN FOR GOVERNMENT AND COMMERCE: DECONSTRUCTING INSECURITY
DEF CON 20 2012 INSECURITY ENGINEERING: GUN SAFES DEFECTIVE DESIGNS
DEF CON 21 2013 ONE OF THE MOST POPULAR LOCKS IN AMERICA
FBI InfraGard Pittsburgh 3D Printing Presentation 2017
Marc Tobias FBI INFRAGARD 2017 LECTURE at the FBI infraGard meeting in Pittsburgh regarding the security issues involving 3D printing technology and the replication and generation of restricted keys for critical infrastructure. See also the information in Secure Content on this site for the lock decoders and government software for generating restricted key profiles.
The PowerPoint deck can be viewed 3D PRESENTATION 12052017 FBI INFRAGARD. Please send an email to request the complete presentation with embedded video and audio if required.
International Lock Picking Competition In 2005 In The Netherlands
The International Competition Where Master Lock-Pickers Do BattleWired
Magazine covered a lock picking competition in the Netherlands where the best of European specialists vied for the fastest times to open locks. This was followed up by a competition in 2008 in Sneek, Netherlands, where the challenge was to open high security cylinders. The best times was :31 seconds.
FBI Charlotte And Microsoft Security Camp 2014 With STEM Students
The FBI Infragard chapter in Charlotte held a five day security camp for STEM high school students on physical and cyber security. Marc Tobias and Tobias Bluzmanis did the first day class in locks and safes and how they work. The students analyze gun safes and handcuffs and other locks, and were able to remove a set of handcuffs from Marc Tobias in about fifteen minutes, using a shim wire. They also figured out how to open Stack-On gun safes that were the subject of a class action lawsuit in 2012, and which could be opened easily by kids. The rest of the week involved cyber security issues that were particularly relevant to high school students.
Yale University Security Seminar 2011
Security Laboratories at Yale University in 2011, Security Summit for two days with Yale and MIT students
Dubai Crime Laboratory Forensic Seminar By Security Labs
A forty-hour course was presented at the Dubai Police Crime Laboratory in Dubai for representatives of seven Middle Eastern countries, including the UAE, Saudi Arabia, and Bahrain. The course was sponsored by the Forensic lab director, Nasser Al Shamshi.
Course material included lock basics, forensic examination, master key theory, and covert entry with specialized government tools.
Wendt Lockmasters Security Group from Germany, and Vicuna from Spain demonstrated the use of different sophisticated government bypass tools for the participants. Presenting were Nasser Al Shamshi, Marc Tobias, Tobias Bluzmanis, Addi Wendt, and Vicuna Tools.
View the photo gallery for a look into the conference and the crime laboratory. Videos in Arabic will be available for foreign participants.
Dubai Forensic Laboratory Seminar by Security Labs And The Dubai Police
Undoing Complexity – From Paper Clips to Ball Point Pens: HOPE 2008
Marc Tobias ans Matt Fiddler lectured at HOPE (Hackers On Planet Earth) in New York about some common tools that are employed to bypass the security of locks.
This talk will be a systematic approach to dissecting and disabling multiple layers of physical security in locks. In this presentation, the focus will be on embedded design defects in high security locks, and how their discovery translates into security vulnerabilities and the disclosure of such flaws. The attack methodology for high security locks will be reviewed. Demonstrations will include case examples, examining tolerance exploitation, code design analysis, and leveraging the interaction of internal components within a locking system to achieve different types of bypass. The application of this program in the development of covert, surreptitious, and forced methods of entry will be examined. Also discussed will be the concept of responsible disclosure upon the discovery of security vulnerabilities, and how this concept applies to both those who discover flaws and to the manufacturer that produces them, and why the same concept becomes a technical, logistical, legal, and financial minefield for manufacturers.
Opening Locks In Five Seconds Or Less: Lock Bumping Lecture At Cambridge 2006
Opening locks by bumping in five seconds or less: is it really a threat to physical security? Marc Weber Tobias gave a lecture at the University of Cambridge Computer Security Lab on the design issues that allowed pin tumbler locks to be opened in seconds. Security Seminar – 23 May 2006_ Marc Weber Tobias, Investigative Law Offices
The subject of lock bumping was introduced at Def Con in 2006 by Marc Tobias and Matt Fiddler. an eleven year old girl, Jenna Lynn demonstrated how to bump open popular locks at the Lock Picking Village and in the lecture by Tobias and Fiddler. watch the video.
The following year she demonstrated how to bump the Medeco high security locks with ARX high security pins. Watch the video. The demonstration was viewed by many experts and verified.
The book “Open in thirty seconds” by Marc Tobias and Tobias Bluzmanis fully explore the ability to bump and pick Medeco and other high security locks.
Iloq Security Analysis And Documentation By Security Labs: 2012
Security Labs, Marc Tobias and Tobias Bluzmanis conducted a detailed examination of the iLoq electronic cylinder produced in Finland. The company had several design errors that allowed us to open these locks in a variety of ways without any evidence of entry.
The design of the locks are very clever and are self-powered, They are extremely popular in the Finland market, and are expanding their reach into other areas of Europe. We produced an animation of each of the components to show how they work together. This video is used for teaching product design.
Illinois State Police Laboratory Lock Forensics: Bill Sherlock Interview
Bill Sherlock was the head of the Forensic Section of the Illinois State Police in Chicago. He was one of the pioneers in the forensic analysis of locks and safes as part of criminal investigations. Watch the video that Bill made with Marc Tobias in Chicago. The material supplements that which is contained in LSS+ Multimedia Edition of Locks, Safes, and Security.
Easy Entrie Milling Machine For Reproducing Blank Keys
The Easy Entrie milling machine was developed in Germany and is capable of replicating or simulating thousands of different key profiles. It is known as the “pink box” and is used by locksmiths and law enforcement agencies to generate blank keys. it will not cut the bitting but simply the profile. Another key machine is used to actually cut the bitting pattern. Marc Tobias and Mahmod Abu Shanab demonstrate how the machine works. There is additional documentation in LSS+ Multimedia edition of Locks, Safes, and Security.
Sensitive Compartmented Information Facility (SCIF): Power Point Presentation
A SCIF is utilized by the United States government to protect confidential information and sensitive conversations. A SCIF is within every federal building that deals in classified materials.
Watch the Power Point presentation on SCIFs.
Lasershield Alarm System: Analysis and Design Flaws
In 2007 Marc Tobias interviewed the engineering team and CEO of Lasershield to discuss the design of their wireless alarm system. It operated at 433 MHz and could easily defeated. The company heavily advertised nationally the security of its products. it was not true.
Read the report on Lasershield. LASERSHIELD_2007
Forced Entry Techniques And Tools: From LSS+ Multimedia Edition
Detailed information about forced entry tools and techniques are disclosed in Locks, Safes, and Security, and in the Multimedia edition. The following material is from LSS+ as a primer. Many videos are shown in LSS+ and in DAME regarding forced entry techniques for locks and safes.
Dubai Police Crime Lab Forensic Series On Locks, Safes, And Covert Entry Tools
The Dubai Police crime laboratory sponsored a forensic conference at their UAE headquarters forty hours of lectures by Marc Weber Tobias, Tobias Bluzmanis, Addi Wendt (Wendt Security Group), and Jose Luis (Vicuna Company). The presentation was made possible by Lt. Nasser Al Shamsi, head of the laboratory.
Investigators and crime lab scientists from seven countries attended. Basic lock design, forensic analysis, and covert entry tools and techniques were presented. Watch the five days of video for different lectures, including an analysis of master key systems.
Day 1 lectures: Forensics
Day 2 Lectures
Day 3 Lectures
Day 4 Lectures: Morning
Day 5 Lectures: Covert entry tools with Wendt Security, and Vicuna
Smirking & Vulnerability Assessments: Roger G. Johnston, Ph.D., CPP
Roger Johnston is the Team Leader at Argonne National Labs near Chicago. This article is about vulnerability assessments and discusses history and goals to discover security flaws and vulnerabilities.
University of Cambridge Department of Computer Science and Technology: Seminars
A schedule of seminars at the Computer Security Lab at Cambridge, from 2010-2020, including lectures by Marc Tobias and Tobias Bluzmanis.
Department of Computer Science and Technology – Security Group_ All
Argonne Vulnerability Assessment
Argonne Vulnerability Assessment Team (2012)
The Argonne National Laboratory has a world renown vulnerability assessment team, which was led by Roger Johnston. They are Internationally recognized in their expertise in tags, seals, access control, anti-counterfeiting,
cargo security, nuclear safeguards, & physical tamper/intrusion detection.
Common Cargo Security Blunders and How to Avoid Them
This article is by Roger G. Johnston, Ph.D., CPP, and Jon S. Warner, Ph.D.
They are with the Vulnerability Assessment Team at Argonne National Laboratory. Read about common cargo security blunders in the following article.
Why Pharma’s Anti-Tampering Strategies Don’t Work: Dr. Roger Johnston
“We’ve never seen what we would consider effective tamper-detection for a drug product,” says Dr. Roger Johnston, head of the Vulnerability Assessment Team as Los Alamos National Laboratories. In this exclusive interview,
Johnston gives us the ten top failings of anti-tampering efforts, and solutions for improvement. Also, click the “Download Now” button at the end of the
article to obtain Johnston’s PowerPoint presentation on improving tamper detection systems.
Why Pharma’s Tamper-Evident Packaging Strategies Don’t Work _ Pharmaceutical Manufacturing
Security in Depth: 2009 Article By Dr. Roger Johnston
Security in Depth is a good thing: 4 layers of security trumps 1 layer of security every time, right? Well, not so fast! Layered security can be a useful tool, but it also holds lots of hidden dangers.
Almost every vulnerability assessor is familiar with the following scenario, which the author has personally witnesses at least 2 dozen times (including at nuclear facilities): A security manager is shown a simple, successful attack on a security device or system, or a portion of the overall security program. Then he/she is shown an inexpensive counter-measure, or at least a partial fix that is relatively painless. The instant response: “Well, yes, that is all very interesting, but we have multiple layers of security, so a failure in one layer does not mean that our overall security has failed. Thus, we don’t need to be concerned with this vulnerability, nor do we need to implement the recommended countermeasure(s).”
Cargo Security Issues: Research on Improving Cargo Security
This is an excellent paper on many facets of cargo security, written by the team at the Los Alamos National Laboratory. It covers seals, RFID, GPS, terminology, tags, and overall security considerations and vulnerabilities.
cargo security issues (2006) Powerpoint Presentation
Layered Security: Self Defense or Self Delusion? By Dr. Roger Johnston
Read the article by Dr. Roger Johnston and the LANL team.
Security in Depth is a good thing: 4 layers of security trumps 1 layer of security every time, right? Well, not so fast! Layered security can be a useful tool, but it also holds lots of hidden dangers.
Almost every vulnerability assessor is familiar with the following scenario, which the author has personally witnesses at least 2 dozen times (including at nuclear facilities): A security manager is shown a simple, successful attack on a security device or system, or a portion of the overall security program. Then he/she is shown an inexpensive countermeasure, or at least a partial fix that is relatively painless. The instant response: “Well, yes, that is all very interesting, but we have multiple layers of security, so a failure in one layer does not mean that our overall security has failed. Thus, we don’t need to be concerned with this vulnerability, nor do we need to implement the recommended countermeasure(s).”
Is this the correct decision? Ultimately, maybe it is and maybe it isn’t. But to knee-jerk the decision not to explore the possibility of improving a given layer or portion of a security program based solely on the idea that there are additional layers is certainly not the right response.
287 Security Blunders You Should Avoid: LANL Vulnerability Assessment Team
The VAT analyzes the most common security blunders. Here are their Top Ten:
1 Lack of Critical/Creative Reviews & AVAs
2 No countermeasures for Cognitive Dissonance
3 Compliance-Based Security
4 Confusing Inventory with Security
5 Confusing Control with Security
6 Thinking that finding vulnerabilities is bad
news & means that somebody has been
screwing up
7 Mindless faith in “Security in Depth”
8 Thinking that all vulnerabilities can be found
& eliminated
9 Focusing on threats instead of vulnerabilities
10 Mindless faith in Technology & Snake Oil
Read the article by Jon S. Warner, Ph.D., Roger G. Johnston, Ph.D., CPP and the Vulnerability Assessment Team Argonne National Laboratory.
287 security blunders (2009)
Countermeasures to Wishful Thinking: Bahrain Lecture
A lecture by Roger Johnston, Ph.D. at Argonne National Labs. He discusses the following myths:
security maxims (there’s no free lunch)
high tech ≠ high security
inventory ≠ security
RFIDs & CMBs
GPS
tamper-indicating seals & cargo security
tamper-evident packaging
biometrics & access control systems
counterfeiting security devices
data encryption/authentication
polygraphs
“security in depth”
effective vulnerability assessments
Read about the common security maxims:
1. Infinity Maxim: There are an unlimited number
of vulnerabilities, most of which will never be
discovered (by the good guys or bad guys).
2. Arrogance Maxim: The ease of defeating a security
device is inversely proportional to how confident the
designer, manufacturer, or user is about it, and to how
often they use words like “impossible” or “tamper-proof”.
3. High-Tech Maxim: The amount of careful thinking that
has gone into a given security device is inversely
proportional to the amount of high-technology it uses
4. Low-Tech Maxim: Low-tech attacks work
(even against high-tech devices).
5. Yipee Maxim: There are effective, simple, & low-cost
countermeasures to most vulnerabilities.
6. Arg Maxim: But users, manufacturers, and
bureaucrats will be reluctant to implement them.
7. Insider Risk Maxim: Most organizations will ignored
or seriously underestimate the threat from insiders.
Anti-Evidence Seals: A Paper By Roger Johnston And Jon S. Warner, Ph.D. In 2006
Summary: Current tamper-indicating seals are WAY too easy
to spoof.
That’s bad because they are protecting important
stuff.
There are workarounds.
But much better seals are both needed and
possible: Anti-Evidence Seals
This article is about anti-tamper seals and how easily they can be defeated.
Advantages of Anti-Evidence Seals: About Tamper Protection
Seals are used in a variety of protective environments. This article explores the use of seals and their often simple bypass.
examples of seal applications
• utility meters
• records integrity
• nuclear safeguards
• waste management
• cargo & port security
• banking & courier bags
• ballots & voting machines
• computer physical security
• loss detection & prevention
• law enforcement & forensics
• protecting medical sterilization
• protecting instrument calibration
• hazardous materials accountability
• protecting food & drugs, etc
Vulnerability Assessment And The Human Factor: A Summary Of Resources
POWERPOINT: VAT and human factors (2009)
VAT human factors research (2010) Article by Roger Johnston and the Vulnerability Assessment Team at LANL.
This article covers:
Nuclear Safeguards
Vulnerability Assessments
Novel Security Approaches
Human Factors in Security
Future Directions in Physical Security
future (2008) Power Point presentation
This is a presentation by Roger Johnston and Jon S. Warner, Ph.D. at LANL. The authors discuss the future direction and technology that will appear in security issues and protection. This includes:
- Wishful thinking about high-tech will only increase.
- As high-tech increases, careful thinking about security will decrease.
- At some point, a terrorist incident will shut down a major U.S. port/s with severe economic & geopolitical implications.
- The RFID allure will die out and will be replaced by true security devices, including RF devices.
- There will be serious GPS spoofing incidents.
Tamper Indicating Seals: How To Do Vulnerability Assessments
how to do seal VAs (2006) Power Point
how to do seal VAs (2006) Presentation
Watch the Powerpoint Presentation by the Team at LANL.
defeating a seal: opening a seal, then resealing (using the original seal or a counterfeit) without being detected. Defeating seals is mostly about fooling people, not beating hardware (unlike defeating locks, safes, or vaults)!
attacking a seal: undertaking a sequence of actions designed to defeat it.
This presentation is by the Vulnerability Assessment Team at LANL (Los Alamos National Labboratory).
New Approaches to Tamper and Intrusion Detection for Safeguards and Transport Security
In this Powerpoint presentation, the LANL Team discusses new approaches regarding tamper intrusion and detection. Definitions are presented, including:
tamper detection: delayed (after the fact) detection of unauthorized access.
intrusion detection: immediate (real-time) detection of unauthorized access.
lock: a device to delay, complicate, and/or discourage unauthorized entry.
seal : a tamper-indicating device (TID) designed to leave non-erasable, unambiguous evidence of unauthorized entry or tampering. Unlike locks, seals are not necessarily meant to resist access, just record that it took place.
tag: a device or intrinsic feature (“fingerprint”) for uniquely identifying an object or container.
defeating a seal: opening a seal, then resealing (using the original seal or a counterfeit) without being detected.
attacking a seal: undertaking a sequence of actions designed to defeat it.
Virtual Numeric Tokens: Roger G. Johnston Ph.D.
Imagine an anti-counterfeiting tag that:
Is inexpensive & unobtrusive.
Is very difficult to counterfeit in large numbers.
Can be automatically checked by wholesalers, retailers, or volume end users (with an inexpensive reader).
Can be checked by consumers (without a reader).
Typically detects more than 98% of the fakes examined.
Effectiveness scales automatically with the level of concern.
Does not become easier to defeat over time, or as technology advances.
Product Authenticity Strategies: Vulnerability Assessment Team At LANL
product authenticity strategies (2012)
product authenticity strategies (2012) Powerpoint
product authenticity talk (2011)
These articles and powerpoint presentations considers different issues involving:
numeric tokens (CNT)
trusted manufacturer & good cargo security
dedicated manufacturing day(s), on-site personnel, courier(s)
buy the manufacturer (maybe team with other end-users)
make he product yourself (maybe team with other end-users)
tags
taggants
measure orthogonal physical properties
product forensic analysis
track & trace
don’t buy brokered, resold, repackaged products
don’t accept low bids or lowest prices
Security Theater In Future Arms Control Regimes: Roger Johnston Ph.D.
See the three different presentations below about the concept of “security theater.”
security theater talk (INMM 2010)
This is a presentation by Roger G. Johnston and Jon S. Warner, Vulnerability Assessment Team, Nuclear Engineering Division, LANL.
ABSTRACT
“Security Theater” (also known as “Ceremonial Security”) involves procedures, policies, and technologies that give the superficial appearance of providing security without actually countering malicious adversaries to any significant degree. As vulnerability assessors, we frequently find Security Theater across a wide range of different physical security devices, systems, and programs,
as well as in domestic and international nuclear safeguards. Security Theater is not automatically a bad thing; it can have its uses. The real problem occurs when Security Theater is not recognized as such, or when it stands in the way of good security or is preferred over real security. In this paper, we present a vulnerability assessor’s view of where future arms control verification regimes are likely to be plagued by Security Theater, based partially on our understanding of current security vulnerabilities and our experience with Security Theater. We also offer suggestions for spotting Security Theater, and for preventing it. Future nuclear safeguards measures that are particularly at
risk for becoming merely Security Theater include tamper-indicating seals and information barriers.
Threats vs. Vulnerabilities
This article discusses “Being Vulnerable to the Threat of Confusing Threats with Vulnerabilities* It was published by the LANL Vulnerability Assessment Team.
threats vs vulnerabilities (2010)
The author begins the article by stating: The following ideas are common, but I think quite wrong and thus myths:
A Threat without a mitigation is a Vulnerability.
A Threat Assessment (TA) is a Vulnerability Assessment (VA).
Threats are more important to understand than Vulnerabilities.
Many of the most common tools used for “Vulnerability Assessments”
(whether true VAs or actually TAs) are good at finding Vulnerabilities.
Countermeasures To Perceptual Blindness: Roger G. Johnston Ph.D.
perceptual blindness (INMM 2010)
perceptual blindness talk (2010)
Perceptual Blindness, also called Inattentional Blindness, is the common phenomenon of a person failing to perceive objects or actions that are in plain sight. Causes beyond just basic human psychology can include not having a mental framework prepared in advance to perceive the objects or actions (that is, not being ready for the unexpected); wishful thinking or denial (due to cognitive dissonance) that prevents someone from seeing what he or she would like not to exist; intense mental focus on certain features which can cause mental distraction in regards to others; or deliberate misdirection by another person.
Fortunately there are potential—though largely untested—
countermeasures to perceptual blindness. These include choosing one or more inspectors or security guards to be the generalist to examine the general scene without specific assigned detailed observational responsibilities; conducting training to improve observational skills; making relevant personnel aware of perceptual blindness issues and demonstrating perceptual blindness to them; using magicians to demonstrate misdirection and sleight-of-hand techniques; engaging in frequent mental “what if” exercises to better mentally prepare observers for the unexpected; and implementing countermeasures to groupthink, denial, cognitive dissonance, and wishful thinking.
Possible results:
There are serious implications for security guards
& safeguards inspectors, especially those who:
check security badges
watch video monitors
make daily rounds
inspect seals
guard gates
operate safeguards equipment
Better Approaches to Physical Tamper Detection
The Vulnerability Assessment Team at LANL has worked hundreds of security problems, including:
Seals & Tamper/Intrusion Detection
Cargo security
First to show how easy it is to spoof, not just jam GPS. First to
suggest countermeasures.
Defeats of a number of different biometric and other access control
devices (many different ways).
Attacks on RFIDs & contact memory buttons
Sticky bomb detection
Demonstrated attacks on an electronic voting machine from the voters’ end.
Product authenticity (especially wine & pharmaceuticals)
Questioning the security of urine drug tests
Better ways to protect logged/monitoring/surveillance data
Nuclear Safeguards
Special Field Tools
Vulnerability Assessments
Consulting & Security Training
Human Factors in Security / Security Culture & Climate
Sticky Bomb Detection with Other Implications for Vehicle Security
sticky bomb detection paper (2010)
This is a paper by Roger G. Johnston Ph.D., Jim Vetrone, and Jon S. Warner from LANL.
A “sticky bomb” is a type of improvised explosive device (IED) placed on a
motor vehicle by (for example) a terrorist. The bomb is typically attached with
adhesive (“duct”) tape, or with magnets. This paper reports some preliminary
results for a very rudimentary demonstration of two techniques for detecting the placement of a sticky bomb on a motor vehicle. There are other possible security applications for these techniques as well.
Don’t Swallow the Snake Oil: Understanding the Vulnerabilities & Limitations of High-Technology
This is a presentation by Roger G. Johnston, Ph.D., CPP and Jon S. Warner, Ph.D., from LANL Vulnerability Assessment Team.
They present a history of snake oil:
Ancient World: medicines made from snakes are believed to have curative powers.
1880: John Greer’s snake oil cure-all.
1893: Clark Stanley (“The Rattlesnake King”) sells his Snake Oil Liniment at the World’s Columbian Exhibition in Chicago. A big hit. Contained mineral oil, camphor, turpentine, beef fat, and chile powder…but no snake extract!
Today: A product is called “snake oil” if it is fake, shoddy, or severely over-hyped.
New Tamper-Indicating Seals
This is an article by Roger G. Johnston, Ph.D., CPP*, Jon S. Warner, Ph.D., Sonia J. Trujillo, Anthony R.E. Garcia, Ron K. Martinez, Leon N. Lopez, and Adam N. Pacheco of the Vulnerability Assessment Team Los Alamos National Laboratory.
Product tampering is a serious product safety issue. Unfortunately,
neither tamper-evident packaging used on consumer products, nor
tamper-indicating seals used for cargo, warehouse, and factory security
provide reliable tamper detection. We believe there is a better approach
to tamper detection, at least for tamper-indicating seals: anti-evidence
seals. Conventional seals must store evidence of tampering until such
time as the seal can be inspected. But adversaries can too easily hide or
erase the evidence, or replace the seal with a counterfeit seal.
With anti-evidence seals, in contrast, we store information when the seal is first installed that tampering has NOT yet been detected. This information
(the “anti-evidence”) gets instantly erased once tampering is detected.
There is thus nothing for an adversary to hide, erase, or counterfeit. This
paper discusses 5 new prototype electronic seals based on the anti-evidence
concept.
Security Advice By Roger G. Johnston, Ph.D. At LANL
In contemplating the use of any new security measure, strategy, or product, you need to determine the correct answers to 3 questions:
(1) To what extend does this really improve security?
(2) What are all the costs, trade offs, and side effects (because there always some)?
(3) Is 1 commensurate with 2?
Assessing the Vulnerability of Tamper-Indicating Seals
This is a paper written by Roger G. Johnston, Ph.D., CPP, Vulnerability Assessment Team, Los Alamos National Laboratory
The Vulnerability Assessment Team (VAT) at Los Alamos National Laboratory
(LANL) has studied tamper detection for 13 years. We have conducted vulnerability assessments (VAs) on hundreds of seals and cargo security programs, and undertaken research and consulting for over two dozen government agencies and private companies. This article discusses how we conduct VAs and what we have learned about seals.
Magical Seals, Secure Voting Machines, and Other Fantasies About Election Security
older election integrity invited talk (2011)
suggestions for better election security (2012)
election security invited talk (2012)
An analysis of election security issues by Roger G. Johnston, Ph.D., CPP and Jon S. Warner, Ph.D.
So Why So Much Bad Physical Security?
Security Theater is easy, thinking and Real Security is hard
Committees, bureaucrats, & knuckleheads are in charge
People & organizations aren’t used to thinking critically about it
Physical Security as a “Taking Out the Garbage” slam dunk thing
“If it’s important, somebody must have thought it through” Myth
Lots of hype, snake oil, & bad products
Blind faith in precedence and “authorities”
Physical security is not a well developed field
Usually we can defeat security devices (including high-tech ones) without attacking the computer/microprocessor, reverse engineering the software, or having an owner’s manual! Might this also be true for electronic voting machines?
Chirping Tag and Seal: 9th Security Seals Symposium Houston, TX, Sept. 2, 2010
This conference presents information on seals and their security. The LANL Vulnerability Assessment Team analyzes many different kinds of seals, including:
customs
cargo security
counter-terrorism
nuclear safeguards
counter-espionage
banking & couriers
drug accountability
records & ballot integrity
evidence chain of custody
weapons & ammo security
tamper-evident packaging
anti-product counterfeiting
medical sterilization
instrument calibration
waste management &
HAZMAT accountability
How To Spot Security Theater: Roger G. Johnston, Ph.D.
how to spot security theater (2010)
Bruce Schneier coined the term “Security Theater” to describe the situation where phony security measures provide a feeling of improved security, but in reality provide little or no actual security.[1,2] Another name for Security Theater is “Ceremonial Security”.
As a vulnerability assessor, I frequently find Security Theater across a wide range of different physical security devices, systems, and programs, as well as in domestic and international nuclear safeguards. It’s important to realize, however, that Security Theater is not automatically a bad thing. It can present the appearance (false though it may be) of a hardened target to potential adversaries, thus potentially discouraging an attack (at least for a while). Security Theater can reassure the public while more effective measures are under development, and help encourage employees and the public to take security seriously.
The Crisis in Physical Security Education: Roger G. Johnston Ph.D., Janie A. Enter, M.S., Ed.S., Eddie G. Bitzer, M.A.
phys security education (2006)
Definition of Physical Security
Protecting valuable tangible assets from harm, or using
physical methods to protect intangible assets. Tangible assets can include, for example, people, equipment, buildings, cargo, money, weapons, museum artifacts, consumer products, food and drugs, medical supplies and equipment, chemicals, hazardous materials, etc.
Intangible can include, for example, computer data, software code,
communications, trade secrets, intellectual property, medical histories and
other sensitive personnel data, instrument calibration, sterility of medical
supplies/equipment, etc.
The “harm” we wish to avoid can include theft, sabotage, tampering, destruction, vandalism, espionage, or counterfeiting. Physical methods for protection can include guards, guns, fences, access control, biometrics, closed-circuit TV cameras, intrusion detectors, locks, safes, vaults, and tamper-indicating seals…plus a lot of other things. Cyber security, cryptography, forensics, and background investigations are
Changing Security Paradigms: Roger G. Johnston Ph.D.
changing security paradigms (2010)
Any field is molded and constrained by its paradigms. A “paradigm” can be defined as:
(1) a pattern, example, or model;
(2) a mode of thought or practice; or
(3) an overall concept or strategy accepted by most people in a given field.
The field of security relies on a number of paradigms, both stated and unstated. Many of these are in the process of changing—or at least should change—in order to adapt to a rapidly changing world and to improve security effectiveness.
Pharma Tampering, Counterfeiting, and Supply Chain Security
There are many widespread mistakes & myths about cargo security and physical security that should be avoided. Current tamper-indicating seals, tamper-indicating packaging, and product anti-counterfeiting tags aren’t very effective.
There’s little sophisticated R&D underway—mostly people and companies
are pushing pet technologies, not trying to solve the problem holistically.
Product counterfeiting and (especially) product tampering are going to get
a lot worse, including terrorist acts.
For many pharma manufacturers, there is a Due Diligence problem for:
tampering & counterfeiting.
Don’t underestimate virtual numeric tokens!
How to be a Better Seal User: Roger G. Johnston Ph.D.
how to be a better seal user (2003)
Tamper-indicating seals have been used for over 7,000 years. Today, seals are widely used to help counter cargo theft, smuggling, sabotage, vandalism, tampering, terrorism, and espionage. Despite their antiquity and modern widespread use, however, there remains considerable confusion about
seals, as well as a lot of misconceptions, wishful thinking, sloppy terminology, and poor practice.
The Vulnerability Assessment Team (VAT) at Los Alamos National Laboratory has intensively studied tamper-indicating seals for the last 12 years. We have provided consulting, vulnerability assessments, and security solutions for over two dozen government agencies and private companies. This article summarizes some of our recommendations for using seals more effectively and with greater sophistication.
An Anti-Counterfeiting Strategy Using Numeric Tokens: Roger G. Johnston Ph.D.
drug anti-counterfeiting (2005)
The counterfeiting of pharmaceuticals continues to be a major worldwide problem, with serious public health and economic consequences. In theory, anti-counterfeiting tags could help to solve this problem. Unfortunately, there are currently no practical, effective tags that significantly resist counterfeiting. This paper discusses a different, relatively low-tech and low-cost approach called the “Call-in the Numeric Token” (CNT) technique. It relies on participation by pharmaceutical customers (possibly including consumers). They check, via phone or Internet, on the validity of the unique, random, unpredictable identity (ID) number assigned to each pharmaceutical container they possess. The numerical container ID is a virtual tag or token, rather than a physical one that is susceptible to counterfeiting.
Counterfeiters are hampered by being unable to guess valid IDs, by being unable to easily acquire large numbers of existing valid IDs, and by being detected when multiple customers report the same IDs. At least some counterfeits can be detected even if only a small percentage of customers participate. The technique is particularly well suited for single-dose (“unit of use”) packaging, but can otherwise be adapted and automated for resellers, wholesalers, re-packagers, and other high-volume customers. While it will not absolutely end counterfeiting, CNT can make pharmaceutical counterfeiting easier to detect and study, and more difficult for counterfeiters. The technique is also applicable to other kinds of products.
Some Comments on Choosing Seals & on PSA Label Seals: Roger G. Johnston Ph.D.
choosing seals and using PSA seals (2006)
Some Comments on Choosing Seals & on PSA Label Seals
Maxims for Choosing Seals!•
There is no best seal. The optimal seal
depends on details of your application
including:!
– Goals!
– Adversaries!
– Consequences of Failure!
– Facilities!
– Personnel!
– Ergonomics !
– Training!
– Containers!
– Hasps & Doors!
– Time & Money Constraints
Under-Utilized Methods for Mitigating the Insider Threat: Roger G. Johnston Ph.D.
insider threat mitigation (2012)
Security Culture & Climate
Security Climate (informal perceptions) is probably even
more important than Security Culture (formal policies &
procedures)
In a healthy security culture/climate:
Everybody is constantly thinking about security.
There are on-the-spot awards for (1) good security practice & (2)
proactive/creative thinking and actions.
Security ideas, concerns, questions, suggestions, criticisms are welcome from any quarter.
No scapegoating! Finding vulnerabilities is viewed as good news.
Physical Security, Security Theater, and Snake Oil: Roger G. Johnston Ph.D.
Physical Security: Scarcely a field at all
You can’t (for the most part) get a degree in it from a major 4-year research university.
– Not widely attracting young people, the best & the brightest.
– Few peer-reviewed, scholarly journals or R&D conferences.
– Lots of Snake Oil & Security Theater.
– Shortage of models, fundamental principles, metrics, rigor,
R&D, standards, guidelines, critical thinking, & creativity.
– Often dominated by bureaucrats, committees, groupthink,
linear/concrete/wishful thinkers, cognitive dissonance.
Physical Security vs. Cyber Security: Which is Dumber? Roger Johnston Ph.D.
The author notes some cyber dumbness:
Failed Electronic Redaction
Inadvertent release of information embedded
inside Office & Acrobat documents
Malicious Thumb Drive in the parking lot problem
(or CD on the desk with a fake IT Department memo)
Susceptibility to Phishing
Security Theater with Adhesive Label Seals
Closed Source
Amateur Hour Cryptography
“It takes a smart man to know he’s stupid. — Barney Rubble, The Flintstones”
Think GPS Cargo Tracking = High Security? Think Again: Roger Johnston Ph.D. and Jon S. Warner, Ph.D.
The Global Position System (GPS) is being increasingly used for a variety of critical applications. These include public safety services (police, fire, rescue and ambulance), marine and aircraft navigation, cargo security, vehicle tracking, and time synchronization for utility, telecommunications, banking, and computer industries.
While people tend to think about GPS as being high-tech and thus high security, the fact is that the satellite signals used in most GPS applications are not secure. The civilian GPS signals—the only ones available to private industry and the vast majority of the federal government—are neither encrypted nor authenticated. They are thus easy to counterfeit, unlike the military GPS signals.
New bottle cap thwarts wine counterfeiters
When the Roman historian Pliny the Elder wrote “in vino veritas” – in wine, there is truth – he must not have been drinking from a counterfeit bottle. Argonne researchers Roger Johnston and Jon Warner have created a device
to ensure that modern wine connoisseurs can have faith that they are drinking what they pay for.
Drill Templates for Safes: DAME Series By Harry Sher
This is an example of one of more than one-hundred videos in the D.A.M.E course taught by Harry L. Sher for locksmiths, government agents, risk managers and security experts. D.A.M.E. is the acronym for Defenses Against Methods of Entry. It is a course that Harry has been teaching for more than twenty years, produced by Marc Weber Tobias. Originally the series was published on disk, and is now online.
Bumping Medeco Locks: Harry Sher Demonstrates The Technique
This is another example of one of the videos in the Defenses Against Methods of Entry series, called DAME, by Harry Sher and produced by Marc Weber Tobias. The series is being updated and placed online.
UNIVERSITY OF CAMBRIDGE LECTURES BY MARC TOBIAS 2007-2024
CAMBRIDGE UNIVERSITY COMPUTER LAB TALKS
Marc Tobias lectured on his new book, Insecurity Engineering, at the University of Cambridge on December 13, 2024. This was his eighth presentation at Cambridge, originally at the invitation of Professor Ross Anderson, who sadly passed away in March, 2024.
A detailed analysis of how locks and physical security become vulnerable to attack 2024
High security locks_ illusion or reality 2007
Insecurity Engineering in Locks 2012
Product Design, Liability, and Insecurity Engineering 2020
Design rules and Maxims for insecurity engineering for lock designs 2022
A detailed analysis of how locks and physical security become vulnerable to attack 2024
Opening locks by bumping in five seconds or less_ is it really a threat to physical security 2006
UNIVERSITY OF RHODE ISLAND FORENSIC LECTURE SERIES; MARC TOBIAS 2005-2022
Marc Tobias lectured at the University of Rhode Island Forensic Series from 2005-2022. See a list of all lectures in this program, organized by Dr. Jimmie Oxley of the Chemistry Department.